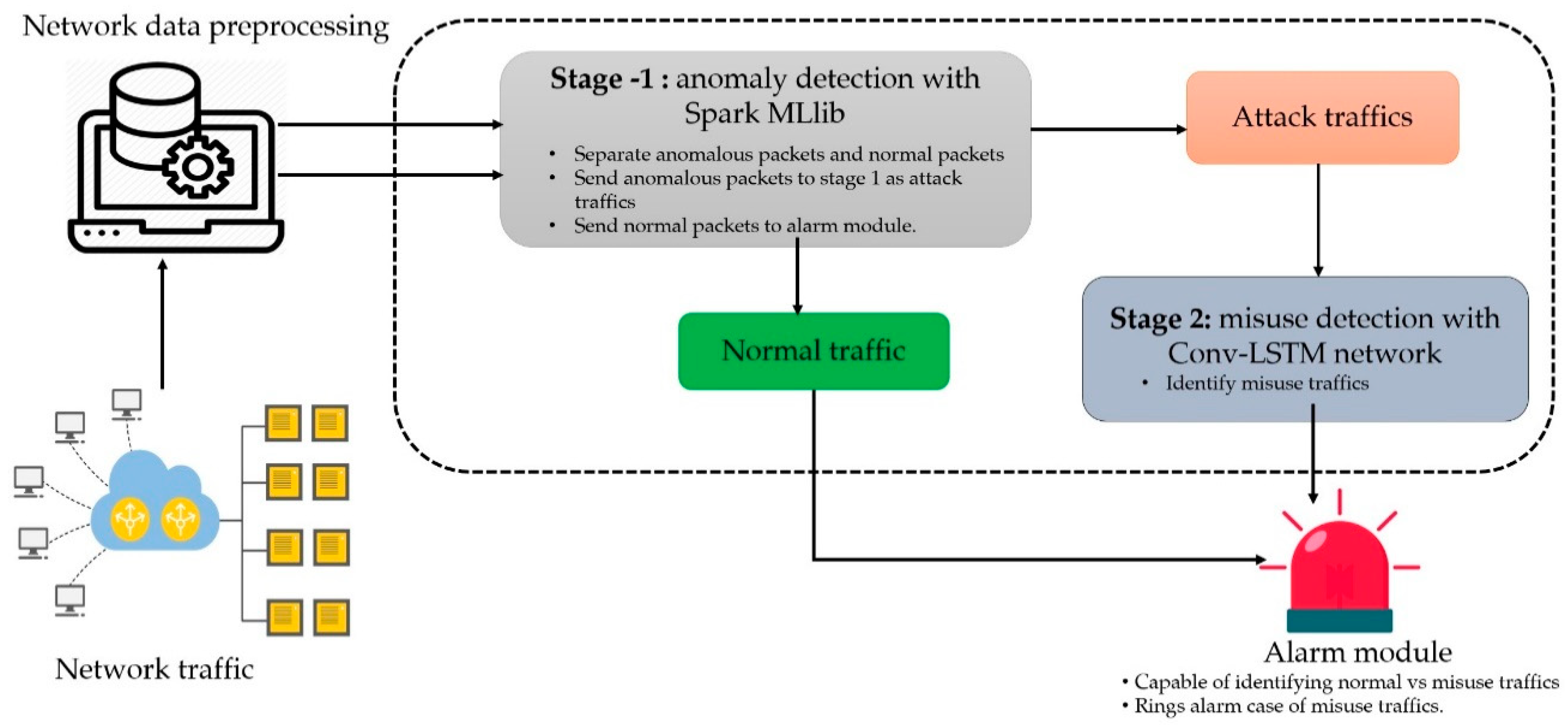
Symmetry | Free Full-Text | A Scalable and Hybrid Intrusion Detection System Based on the Convolutional-LSTM Network
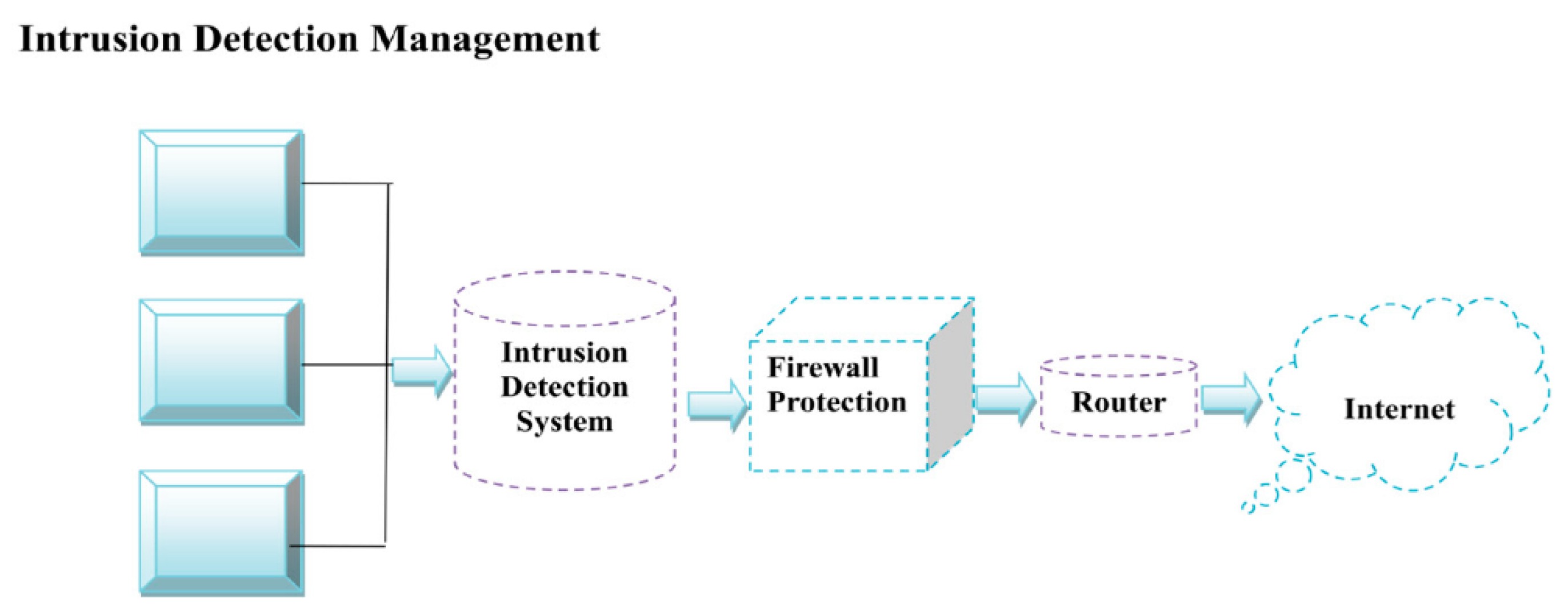
Securing the Internet of Things with Intrusion Detection Systems - BPI - The destination for everything process related

Network intrusion detection system: A systematic study of machine learning and deep learning approaches - Ahmad - 2021 - Transactions on Emerging Telecommunications Technologies - Wiley Online Library

An Exhaustive Research on the Application of Intrusion Detection Technology in Computer Network Security in Sensor Networks
![PDF] Intrusion Detection in the Era of IoT: Building Trust via Traffic Filtering and Sampling | Semantic Scholar PDF] Intrusion Detection in the Era of IoT: Building Trust via Traffic Filtering and Sampling | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/e3bdfd5a2fd2672dacfd34a5e402b68b9283e16f/3-Figure2-1.png)
PDF] Intrusion Detection in the Era of IoT: Building Trust via Traffic Filtering and Sampling | Semantic Scholar

Intrusion Detection with Artificial Neural Networks: Anomaly based Intrusion Detection using Backpropagation Neural Networks: Hossain, Moazzam: 9783639210385: Amazon.com: Books

An improved malicious code intrusion detection method based on target tree for space information network - Chundong She, Yaqi Ma, Jingchao Wang, Luting Jia, 2017
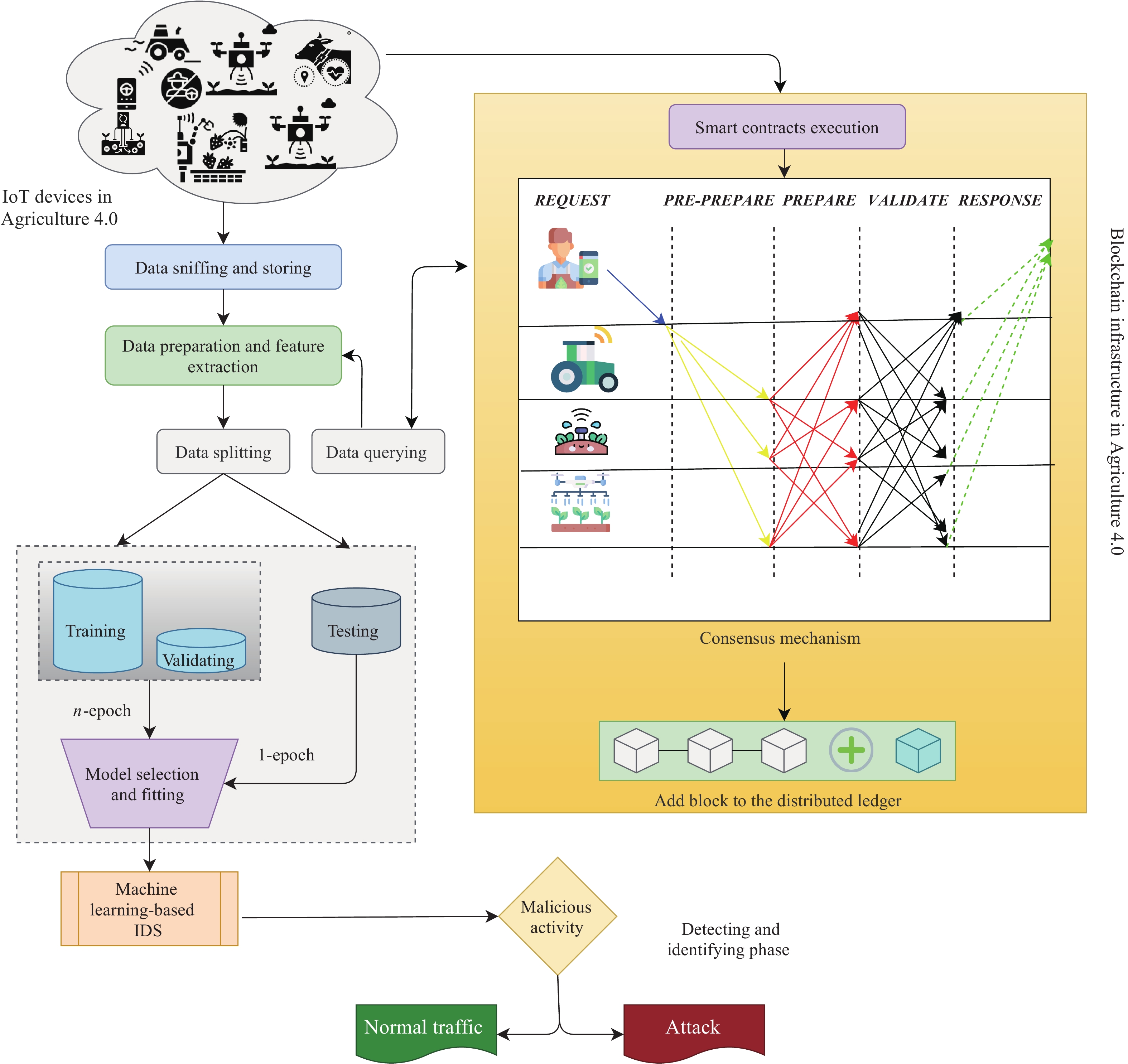
Cyber Security Intrusion Detection for Agriculture 4.0: Machine Learning-Based Solutions, Datasets, and Future Directions

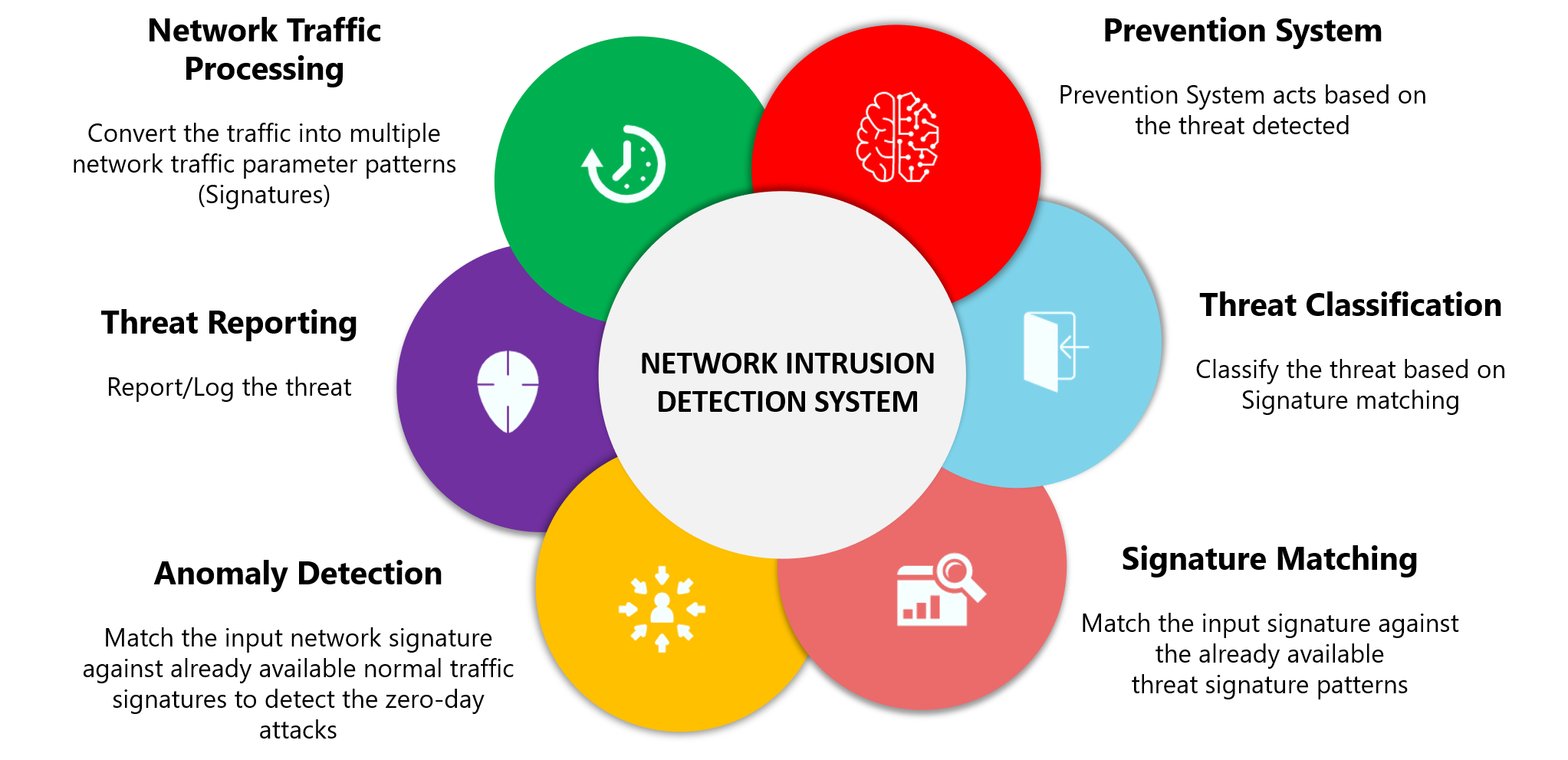
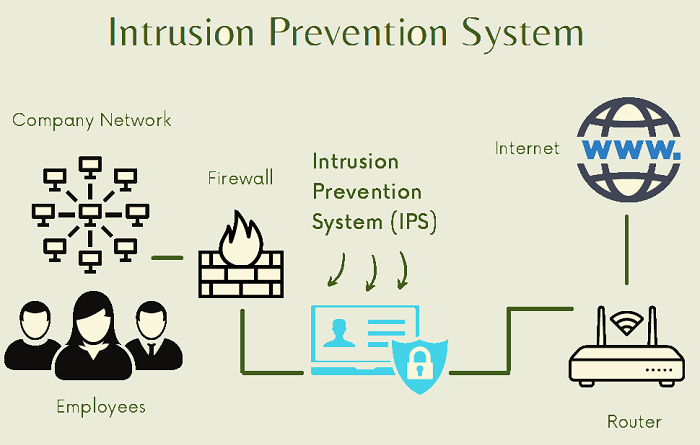
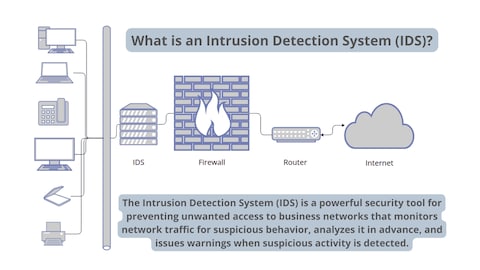
What Is Intrusion Detection and Prevention System? Definition, Examples, Techniques, and Best Practices - Spiceworks






![PDF] Intrusion Detection Systems, Issues, Challenges, and Needs | Semantic Scholar PDF] Intrusion Detection Systems, Issues, Challenges, and Needs | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/6612eb4f569736d1ddb0e93b815a55f8ac815133/2-Figure1-1.png)

![Network intrusion detection using oversampling technique and machine learning algorithms [PeerJ] Network intrusion detection using oversampling technique and machine learning algorithms [PeerJ]](https://dfzljdn9uc3pi.cloudfront.net/2022/cs-820/1/fig-1-2x.jpg)